Topic Overview
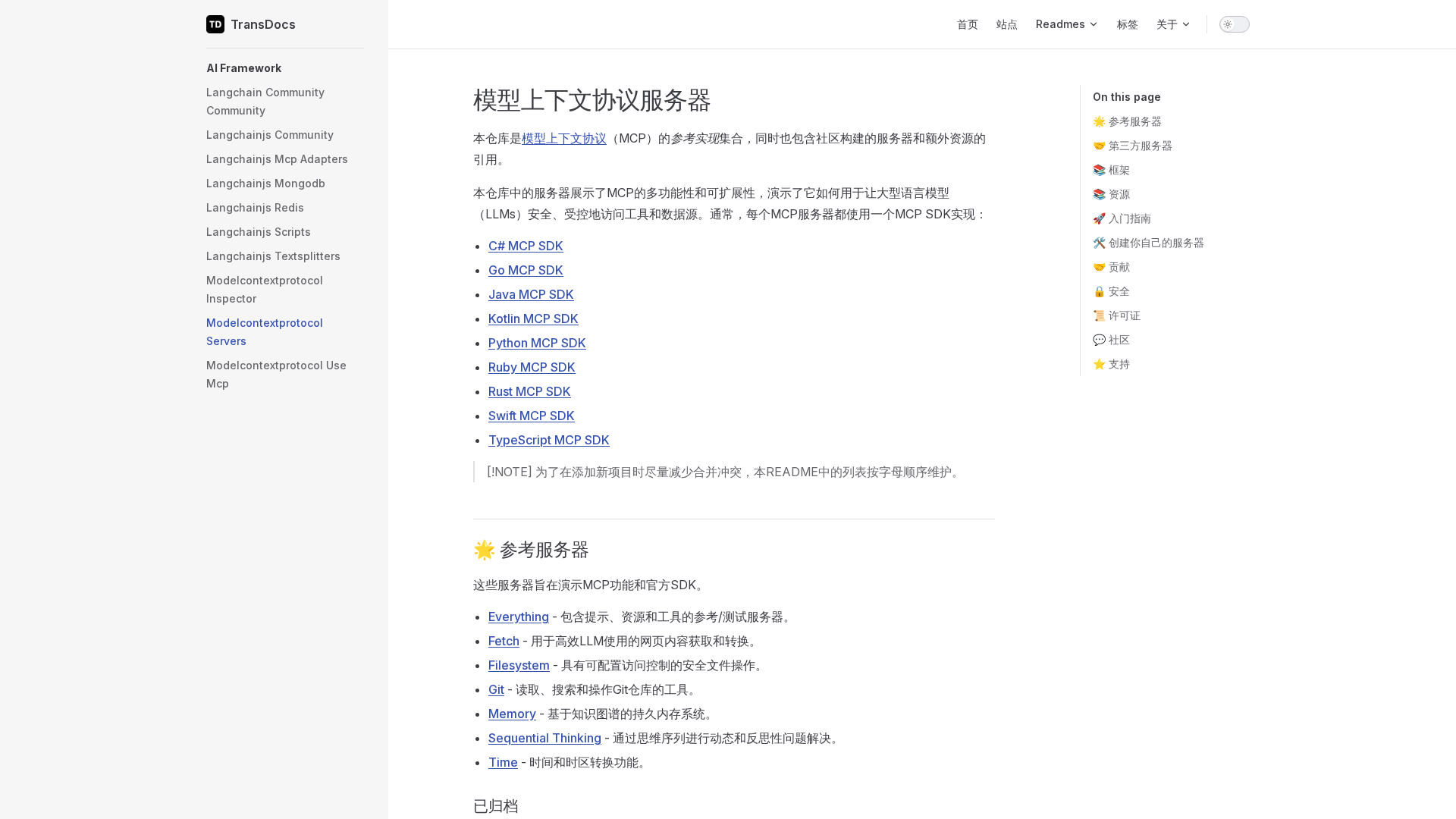
This topic covers the standards and protocol stack needed to enable trustless commerce between AI agents and human users—where value, credentials and data are exchanged with verifiable guarantees rather than blind trust. It centers on credential management patterns (verifiable credentials, keys, attestations) and interoperable interfaces that let AI assistants request cryptographic operations, data reveals, or payments without direct exposure to secrets. Relevance: as of 2026-03-12, deployments of autonomous agents and assistant-driven workflows increasingly require auditability, privacy controls, and minimal-trust settlement. That drives demand for standardized on-chain/off-chain contracts (e.g., ERC‑8183-style norms), remote attestation, and managed key services that keep secrets off agents while enabling provable actions. Key tools and roles: Model Context Protocol (MCP) servers are a common abstraction here—bridging LLMs/agents to credential and key-management backends. Examples in this category include an Attestable MCP that runs inside a trusted execution environment (Gramine + Intel SGX) and issues RA‑TLS-backed certificates; Thales CipherTrust Manager MCP for centralized key lifecycle and cryptographic ops; Thales CDSP CRDP MCP for controlled data-protection reveals; Thales CDSP CAKM MCP for database EKM and TDE operations; and a Keycloak MCP that exposes identity and admin functions. Together they implement separation of duties: agents make signed requests, MCPs invoke protected hardware or HSM-backed services, and on-chain standards record intent and settlement. Trends and implications: practical systems combine hardware attestation, verifiable credentials, EKM/TDE, and compact protocol specs to enable interoperable, auditable commerce while reducing liability. Standards like ERC‑8183 and peer MCP conventions seek to codify these interactions so agents, wallets, KMS/HSMs, and identity providers can interoperate without leaking secrets.
MCP Server Rankings – Top 5

MCP server in a trusted execution environment with RA-TLS attestation.

MCP server for Thales CipherTrust Manager integration, enabling secure key management and cryptographic operations.

MCP server enabling AI apps to protect and reveal data via CipherTrust CRDP.

An MCP server for Database EKM and TDE operations via CipherTrust CAKM.

A Model Context Protocol (MCP) server that provides programmatic access to Keycloak administration functionality.